Simple, Fast, and Compact Folder Permissions Analysis With TreeSize
TreeSize offers you the opportunity to analyze NTFS folder permissions within a scanned directory.
With TreeSize you'll be able to:
- Display general folder and file NTFS permissions
- Display all inherited and non-inherited permissions separately
- Get a clear and compact overview of the allowed and denies permissions
- Export all collected data to Excel or to an HTML, XML, or text file for further processing
The column "Own Permissions" only shows the non-inherited permissions. In contrast, the column "Inherited Permissions" shows those permissions that were passed on e.g. to newly created folders. Thus, you can quickly identify folders which did not inherit all their permissions from their parent directories.
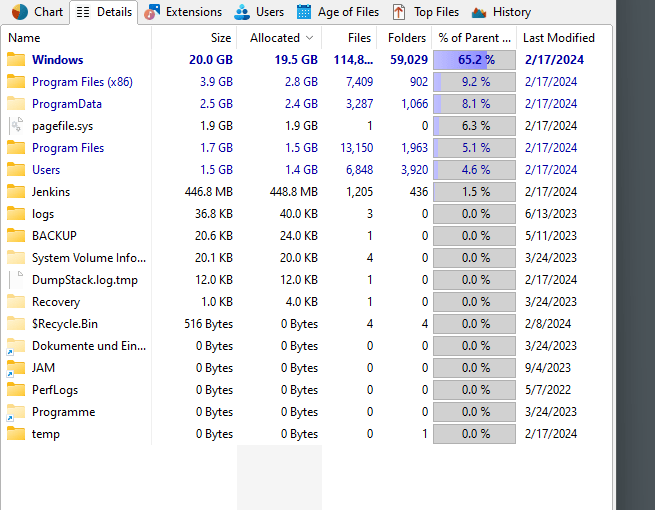
TreeSize presents the owner of each folder and file as well as all applicable permissions in a clear, compact, and easy to read format.
TreeSize also allows you to export all scan results into several data formats such as HTML, XML, text file, or even Excel. You'll be able to create further analysis or special reports which may be used e.g. for security audits.